AI Guardrails for Transparency & Explainability: The New Rulebook for Responsible AI Governance

.png)
Key Takeaways
1. Introduction
For years, companies treated model training data like a trade secret. That worked — until generative AI went mainstream.
In late 2023, The New York Times filed a lawsuit against OpenAI and Microsoft, claiming its reporting had been used to train large language models without permission. What made the case explosive wasn’t just copyright. It was the uncomfortable spotlight it put on training data opacity. When asked what specific content shaped model behavior, there was no clean, auditable list.
That’s where AI transparency stops being a buzzword and starts becoming infrastructure. If organizations cannot trace where their systems learned from, they cannot defend how those systems behave. And if outputs resemble protected material, weak documentation becomes a governance failure.
This is the practical side of AI explainability. It’s not only about interpreting predictions. It’s about being able to justify data sources, model lineage, and decision pathways under scrutiny.
Boards, regulators, and enterprise buyers are now asking harder questions — and vague answers aren’t enough.
2. Breaking Down Transparency and Explainability in AI Systems
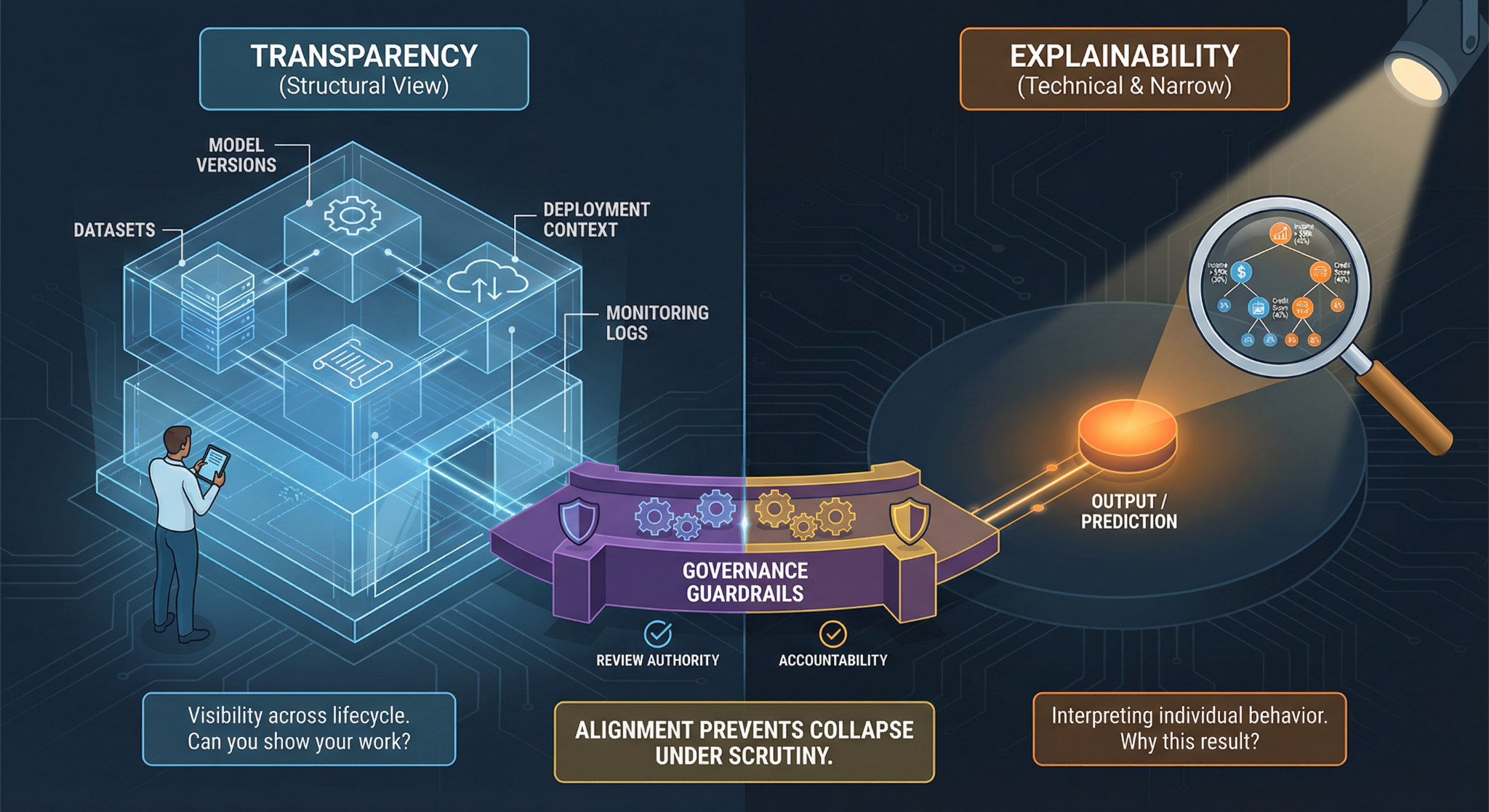
People often use AI transparency and AI explainability as if they mean the same thing. They don’t. And mixing them up creates blind spots.
Start with transparency. It’s structural. It asks: What is this system? Who approved it? What data shaped it? When was it last changed? Transparency is about visibility across the lifecycle — datasets, model versions, deployment context, monitoring logs. If an auditor walks in tomorrow, transparency determines whether you can show your work.
Explainability is narrower — and more technical. AI explainability focuses on individual outputs. Why did the model produce this prediction? Why was that applicant rejected? Why did the chatbot respond in that way? It’s about interpreting behavior, not just documenting existence.
Here’s the catch: you can have explainability without real transparency. A model might generate feature importance scores, yet no one can trace the origin of its training data. That’s where AI governance guardrails matter. They force alignment between documentation, interpretability, review authority, and accountability.
Without that alignment, systems look controlled on paper — but collapse under scrutiny.
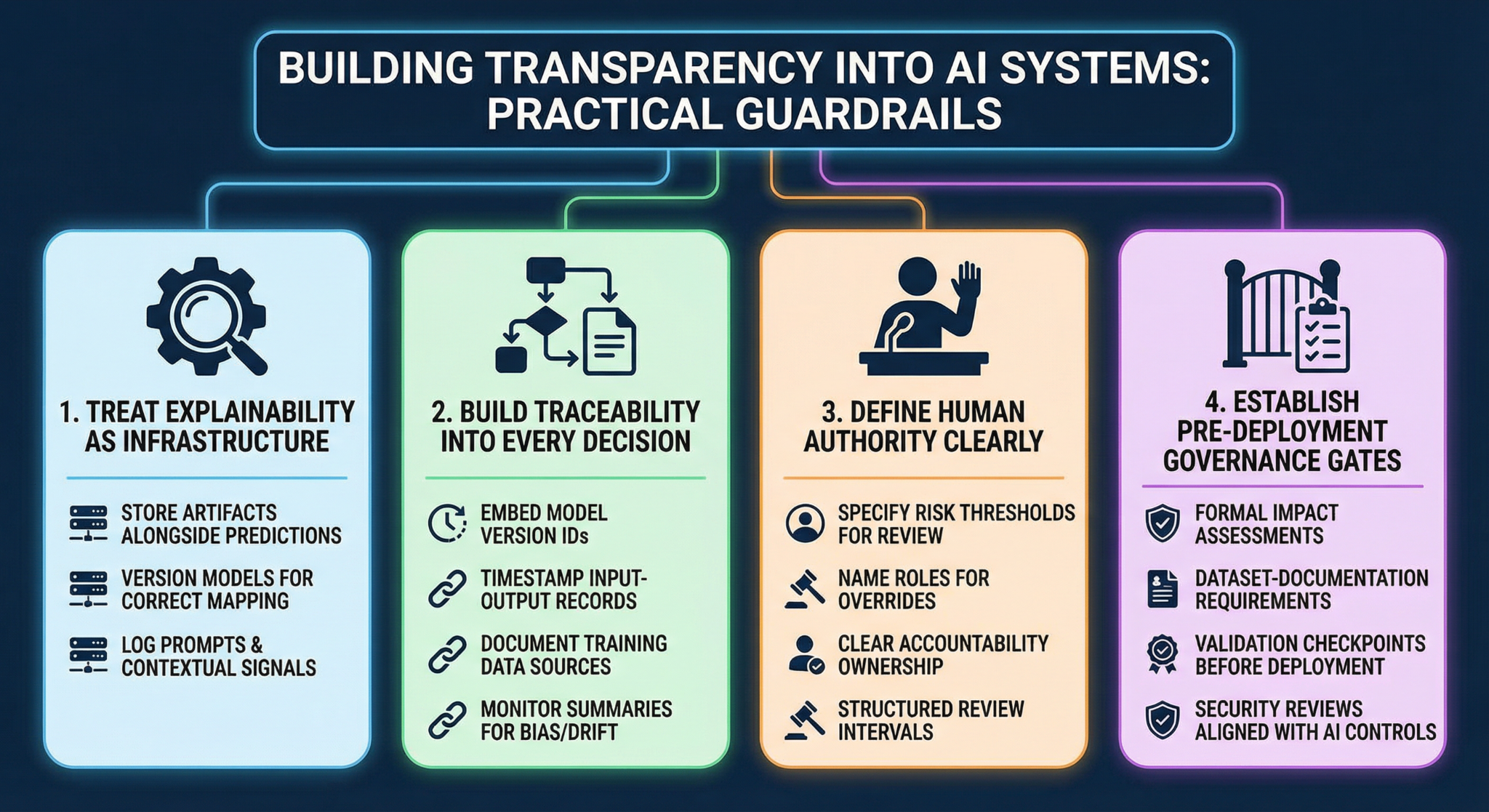
3. Building Transparency into AI Systems: Practical Guardrails
Most AI failures don’t start with bad intent. They start with missing structure. Teams ship fast, models perform well in testing, dashboards look clean — and no one asks how the system would hold up under external scrutiny.
Making AI transparency real requires deliberate engineering choices.
3.1 Treat Explainability as Infrastructure
Plenty of teams experiment with AI model explainability tools during development. Few integrate them into live systems.
In production, that means:
⮞ Storing explanation artifacts alongside predictions
⮞ Versioning models so explanations map to the correct release
⮞ Logging prompts and contextual signals for generative systems
⮞ Recording confidence or uncertainty indicators
If an output is challenged six months later, the explanation should be reproducible. Otherwise, AI explainability becomes a slide deck concept — not an operational capability.
3.2 Build Traceability Into Every Decision
Transparency collapses when systems cannot reconstruct history.
Strong traceability includes:
⮞ Model version IDs embedded in logs
⮞ Timestamped input-output records
⮞ Clear documentation of training data sources
⮞ Monitoring summaries for bias and drift
This is how AI transparency becomes defensible. You are not guessing what happened — you can show it.
3.3 Define Human Authority Clearly
Automation without “escalation” paths creates governance gaps.
High-impact systems should specify:
⮞ “Risk thresholds” that trigger manual review
⮞ Named roles responsible for overrides
⮞ Clear “accountability” ownership
⮞ Structured review intervals
Without defined intervention points, insight from explainability never translates into corrective action.
3.4 Establish Pre-Deployment Governance Gates
How do AI governance guardrails prevent downstream crises?
They introduce friction before release.
Examples include:
⮞Formal impact assessments
⮞ Dataset-documentation requirements
⮞ Validation “checkpoints before deployment
⮞ Security reviews aligned with overall “AI security controls”
When guardrails are embedded early, organizations avoid retrofitting transparency after controversy emerges.
4. Where Transparency Quietly Unravels
Let’s drop the theory for a second.
A system is live. It’s making thousands of decisions a day. No one’s panicking. Everything looks stable.
Then a customer disputes an outcome.
The team pulls logs. They’re incomplete. Someone checks version history. It’s unclear which training snapshot was active. A few engineers try to reconstruct the timeline from deployment notes.
That’s how AI transparency actually breaks — not through scandal at first, but through ambiguity.
When Change Outpaces Control
Models evolve faster than governance routines. New data flows in. Hyperparameters get tuned. Infrastructure shifts.
If those changes aren’t tightly tracked, the system becomes historically opaque. You can describe what it does now, but not what it did then. That gap matters when accountability is required.
When Explanations Don’t Change Outcomes
You might have interpretability layers. Attribution scores. Confidence metrics.
But here’s the real test: does anyone have authority to halt deployment based on those signals?
Without decision rights attached to explanation outputs, AI explainability becomes informational rather than corrective. The organization sees potential issues — and proceeds anyway.
When Security Teams Lack Lineage
During an anomaly, investigators need context. Was the shift caused by new data? Configuration drift? Prompt abuse?
If traceability is thin, diagnosis slows. And slow diagnosis increases exposure.
Transparency doesn’t fail loudly. It fails when clarity is needed most — and isn’t there.
5. What Companies Are Trying — and Where It Falls Short
If you look across large enterprises right now, you’ll see three common reactions to the transparency problem.
First, heavy investment in AI model explainability tools. Dashboards are built. Attribution reports are generated. Monitoring panels track model behavior. That’s useful — but tools don’t create accountability. If no one is required to review those outputs regularly, the system remains exposed.
Second, documentation pushes. Teams draft model cards, policy statements, and internal compliance memos. This improves baseline AI transparency, but documentation ages quickly. If logs and version controls aren’t automatically synced with those documents, accuracy decays over time.
Third, regulation-driven compliance. Organizations respond to audits, answer questionnaires, and adjust language when laws change. That approach protects against immediate penalties, yet it rarely strengthens architecture.
The real gap? Alignment. Transparency data, explanation outputs, review authority, and escalation pathways must operate under formal AI governance guardrails. When they function independently, they create visibility without control.
Bringing them together is what shifts organizations from reactive defense to structured governance.

6. Making Transparency Stick
Let’s be honest — most governance failures aren’t philosophical. They’re procedural. Someone assumed logging was enabled. Someone thought documentation was updated. No one checked.
If AI transparency is critical, it cannot depend on goodwill. It has to be enforced at release time. No model deployment without verified version history. No dataset refresh without lineage updates. No silent configuration changes.
Then there’s the uncomfortable part: what happens when explanation outputs show risk?
If a “bias” metric spikes or output behavior shifts.. who has the authority to pause the system? If no one can intervene, AI explainability is cosmetic. Real governance requires decision rights tied to those signals.
Security alignment matters too. Drift detection, access control changes, and training updates should be reviewed together. When these streams stay disconnected, gaps widen.
And finally — cadence. Scheduled reviews. Named accountability. Measurable thresholds. That’s where AI governance guardrails become durable instead of decorative.
Transparency isn’t built through policy statements. It’s built through constraints that teams cannot bypass.
7. Conclusion
Strip away the compliance language and the lawsuits, and the issue becomes simple: can you defend your system under pressure?
That’s the real test of AI transparency. Not whether a policy exists, but whether a decision can be reconstructed clearly, with evidence.
The same applies to AI explainability. If a high-impact output affects a customer, employee, or citizen, the organization must be able to justify how and why it occurred. Vague technical summaries won’t hold up in courtrooms, audits, or public scrutiny.
The shift happening now is structural. Transparency is moving from “good practice” to baseline expectation. Regulators demand it. Enterprise buyers ask about it. Security teams depend on it.
Organizations that treat transparency and explainability as core infrastructure gain resilience. Those that treat them as documentation exercises eventually face exposure.
The difference isn’t sophistication. It’s preparedness.

AI will only be trusted when it can be understood — transparency is the bridge between intelligence and integrity

.svg)




.png)
.svg)

.png)
.png)



